- Version
- Download 9
- File Size 444.33 KB
- File Count 1
- Create Date 24/04/2026
- Last Updated 24/04/2026
MCP-Driven RAG Architecture for Automated Alert Triage in Security Operations Centers
1.Tisha Patel, 2.Payal Kuvar
Computer Engineering Department, Gandhinagar University, Gandhinagar, Gujarat, India. Computer Engineering Department, Gandhinagar University, Gandhinagar, Gujarat, India.
Abstract
Security Operations Centers (SOCs) are the first line of defense against cyber threats, but they are becoming more and more overwhelmed by the large number and complexity of alerts that modern enterprise infrastructure generates. Surveys of the industry show that false-positive rates in enterprise SIEM deployments often go over 60%. This constant noise makes analysts tired, lowers the quality of decisions, and gives attackers chances to work without being seen. Rule-based correlation engines, supervised machine learning classifiers, and SOAR platforms are some of the current solutions. They only solve part of the problem, and they all have a major flaw: they can't automatically add new threat intelligence, and none of them give clear reasons for triage decisions. This paper presents a unified architecture that integrates the Model Context Protocol (MCP) with a Retrieval-Augmented Generation (RAG) pipeline to facilitate intelligent, explainable, and real-time alert triage in Security Operations Center (SOC) settings. Anthropic released MCP as an open standard in November 2024 [10]. It is a standardized JSON-RPC 2.0 integration layer that links an LLM reasoning engine to CVE databases, the MITRE ATT&CK knowledge base, curated incident repositories, and live threat intelligence feeds. RAG gives the model relevant external context at inference time without having to retrain it. The LLM then makes structured triage decisions and gives analysts step-by-step reasoning chains that they can check, change, and learn from.
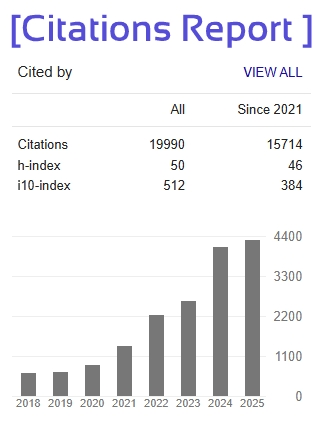
A proof-of-concept implementation was evaluated using the CICIDS2017 benchmark dataset [7] through a reproducible simulation pipeline that produced a corpus of 47,312 synthetic SIEM alerts. Important Caveat: All performance metrics reported in this paper are from the proof-of-concept implementation within a simulation pipeline running on 2017-era network traffic and are not production performance claims. The 61.4% simulation-generated baseline FPR was generated within the simulation itself and was not validated against an actual SIEM deployment. All reported improvements over baselines should be understood relative to this simulation-generated FPR only. Within these limits, the proposed system achieved a FPR, TPR, and a mean triage latency of 3.91 ± 0.52 seconds. All gains over three baseline configurations are statistically significant (p < 0.001 via two-proportion z-test). The overall score in the explainability assessment from three certified SOC analysts was 4.6/5.0, which is not generalizable outside of this group and should be considered only as an initial indication of explainability until further, larger studies (n >= 30) are completed. Component-level latency is discussed based on profiling and attributed to the use ofMCPresponse caching(meancache-hit rate 62.3%)andstructuredcontext prompt compression.The RAG-only baseline did not utilize equivalent caching, thus partially confounding comparison. Contemporary attack dataset evaluation was prioritized as a target for future work.